
The most prominent components of web applications that intruders will first seek to exploit are vulnerabilities within the web platform. The web platform commonly includes: Web server software (such as IIS or Apache)….
Read more
The below questions and answers are designed to both measure your understanding of the concepts of XSS -Cross Site Scripting Attacks and Prevention. Q1: What is the difference between HTML Injection and XSS?…
Read more
Those of us who have conducted or participated in a penetration test will understand that tools are not the only thing necessary to successfully complete a PenTest. Methodologies are essential for ensuring that…
Read more
Web Application Proxies like Burp Proxy, WebScarab or Tamper Data Addon allow a security tester to intercept the requests/responses between the client HTTP application and the web server. Proxies are the fundamental for…
Read more
Security is a state in which we ensure a proper gap between the threats and assets of an organization. We try to either move assets far away from threats or we try to…
Read more
Penetration testing (also called pen testing) is the practice of testing a computer system, network or Web application to find vulnerabilities that an attacker could exploit. Here we’re listing out the quick cheatsheet…
Read more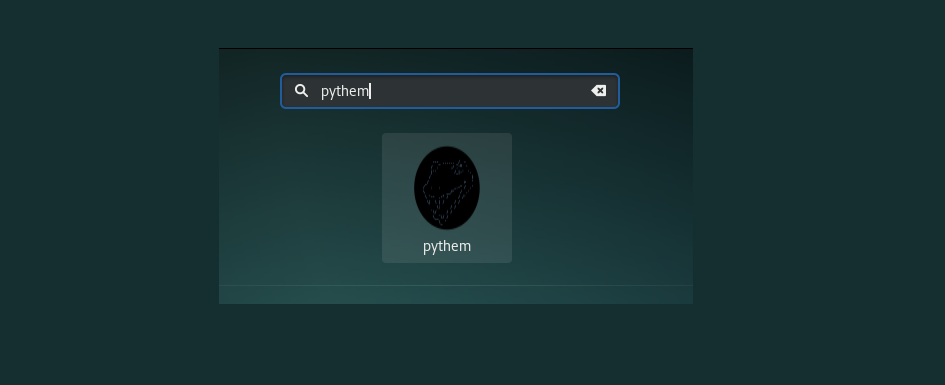
Pythem is a multi-purpose pentest framework written in Python. It has been developed to be used by security researchers and security professionals. The tool intended to be used only for acts within the…
Read more
1. AFE – Android Framework for Exploitation, is a framework for exploiting android based devices. They’ve been in the security field from past 5 years and having a strong enthusiastic team behind Appknox(https://www.appknox.com)…
Read more
Client Side – Static and Dynamic analysis Test Name Description Tool OWASP Applicable Platform Result Reverse Engineering the Application Code Disassembling and Decompiling the application, Obfuscation checking apktool, dex2jar, Clutch, Classdump M10 All…
Read more
For every businessman, development of website is much important as it acts as a most important promotional tool for his products and services. By Developing a website means, your website should be secured…
Read more
Penetration testing involves the use of a variety of manual and automated techniques to simulate an attack on an organization’s information security arrangements. One of the key points when managing testers is to…
Read more



